Two-factor authentication is a great method for making logins more secure.1 Although this system is straightforward, I’ve occasionally made a pretty stupid error while using it. Thankfully, it’s an error that can be easily prevented with a simple fix.
Most of the websites, for which I have set up two-factor authentication, send authentication codes to my phone. For privacy reasons, I have configured my phone to notify me of incoming text messages; the notifications will not display the messages’ content, though. That way, if I leave the phone on my desk, someone who walks by can see that I received a message, but won’t be able to read what it’s about.
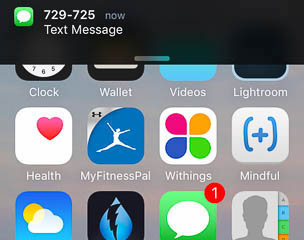
The numbers, from which the codes are sent, usually are six digits long. The authentication codes are six digits long, too. You can already guess where this is going.
If I don’t pay attention, I sometimes enter the phone number instead of the actual authentication code, because that’s what catches my eyes when I look at the notification. On one occasion, I was so distracted that I actually panicked about being locked out from one of my accounts. Until it dawned on me what I had done wrong.
It would be very easy to prevent this error. All it takes is a comparison of the entered code with the phone number. If the system finds a match between the user’s entry and a phone number, it would display a message to make the user aware of their mis-hap.
This simple fix would go a long way in keeping users’ heart rate and blood pressure within healthy limits.
-
The concept behind two-factor authentication is simple: In addition to the usual username and password credentials, you need to provide additional authentication that is usually linked to another hardware device. E.g., when you log into a website with your username and password, the site texts a code to a mobile phone. To complete the login process, you then need to enter that code. This means that you can only log in if you have know the username and password and you have access to the phone that receives the codes. To learn more, read the Wikipedia article on two-factor authentication. ↩